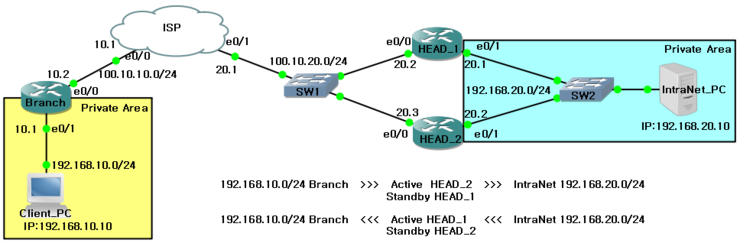
IPSec VPN – HSRP
IPsec과 VPN을 운용함에 있어 장비 및 회선에 따라서 발생할 수 있는 물리적인 장애에 대비하기 위하여
HSRP를 IPsec VPN과 조합하여 사용하도록 한다.
본 실습에선 각각의 사설구간(192.168.10.0/24, 192.168.20.0/24)에서 출발지에 따라서 Active / Standby 역할을
하는 라우터가 달라지도록 HSRP를 구성하고자 한다.
■ 실습 토폴로지
1. 통신 기본 설정
■ ISP 라우터
Router(config)# hostname ISP
ISP(config)# interface ethernet 0/0
ISP(config-if)# ip address 100.10.10.1 255.255.255.0
ISP(config-if)# no shutdown
ISP(config-if)# exit
ISP(config)# interface ethernet 0/1
ISP(config-if)# ip address 100.10.20.1 255.255.255.0
ISP(config-if)# no shutdown
ISP(config-if)# exit
ISP(config)# router eigrp 10
ISP(config-router)# no auto-summary
ISP(config-router)# network 100.10.10.0
ISP(config-router)# network 100.10.20.0
■ BRANCH 라우터
Router(config)# hostname Branch
Branch(config)# interface ethernet 0/0
Branch(config-if)# ip address 100.10.10.2 255.255.255.0
Branch(config-if)# no shutdown
Branch(config-if)# exit
Branch(config)# interface ethernet 0/1
Branch(config-if)# ip address 192.168.10.1 255.255.255.0
Branch(config-if)# no shutdown
Branch(config-if)# exit
Branch(config)# router eigrp 10
Branch(config-router)# no auto-summary
Branch(config-router)# network 100.10.10.0
사설구간 네트워크 192.168.10.0/24은 eigrp에 지정하지 않는다.
■ HEAD-1 라우터
Router(config)# hostname HEAD-1
HEAD-1(config)# interface ethernet 0/0
HEAD-1(config-if)# ip address 100.10.20.2 255.255.255.0
HEAD-1(config-if)# no shutdown
HEAD-1(config-if)# exit
HEAD-1(config)# interface ethernet 0/1
HEAD-1(config-if)# ip address 192.168.20.1 255.255.255.0
HEAD-1(config-if)# no shutdown
HEAD-1(config-if)# exit
HEAD-1(config)# router eigrp 10
HEAD-1(config-router)# no auto-summary
HEAD-1(config-router)# network 100.10.20.0
사설구간 네트워크 192.168.20.0/24은 eigrp에 지정하지 않는다.
■ HEAD-2 라우터
Router(config)# hostname HEAD-2
HEAD-2(config)# interface ethernet 0/0
HEAD-2(config-if)# ip address 100.10.20.3 255.255.255.0
HEAD-2(config-if)# no shutdown
HEAD-2(config-if)# exit
HEAD-2(config)# interface ethernet 0/1
HEAD-2(config-if)# ip address 192.168.20.2 255.255.255.0
HEAD-2(config-if)# no shutdown
HEAD-2(config-if)# exit
HEAD-2(config)#
HEAD-2(config)# router eigrp 10
HEAD-2(config-router)# no auto-summary
HEAD-2(config-router)# network 100.10.20.0
사설구간 네트워크 192.168.20.0/24은 eigrp에 지정하지 않는다.
2. IPsec VPN phase 1 설정
■ Branch 라우터
Branch(config)# crypto isakmp policy 10
Branch(config-isakmp)# authentication pre-share
Branch(config-isakmp)# hash sha
Branch(config-isakmp)# encryption aes 128
Branch(config-isakmp)# group 2
Branch(config-isakmp)# exit
Branch(config)#
Branch(config)# crypto isakmp key 6 cisco address 100.10.20.254
Branch(config)# crypto isakmp keepalive 10
■ HEAD-1 라우터
HEAD-1(config)# crypto isakmp policy 10
HEAD-1(config-isakmp)# authentication pre-share
HEAD-1(config-isakmp)# hash sha
HEAD-1(config-isakmp)# encryption aes 128
HEAD-1(config-isakmp)# group 2
HEAD-1(config-isakmp)# exit
HEAD-1(config)#
HEAD-1(config)# crypto isakmp key 6 cisco address 100.10.10.2
HEAD-1(config)# crypto isakmp keepalive 10
HEAD-1(config)#
■ HEAD-2 라우터
HEAD-2(config)# crypto isakmp policy 10
HEAD-2(config-isakmp)# authentication pre-share
HEAD-2(config-isakmp)# hash sha
HEAD-2(config-isakmp)# encryption aes 128
HEAD-2(config-isakmp)# group 2
HEAD-2(config-isakmp)# exit
HEAD-2(config)#
HEAD-2(config)# crypto isakmp key 6 cisco address 100.10.10.2
HEAD-2(config)# crypto isakmp keepalive 10
HEAD-2(config)#
3. IPsec VPN phase-2 설정
■ Branch 라우터
Branch(config)# access-list 110 permit ip 192.168.10.0 0.0.0.255 192.168.20.0 0.0.0.255
Branch(config)# crypto ipsec transform-set IntraNet ah-sha-hmac esp-aes 128
Branch(cfg-crypto-trans)# exit
Branch(config)#
Branch(config)# crypto map To-HEAD 10 ipsec-isakmp
Branch(config-crypto-map)# set peer 100.10.20.254
Branch(config-crypto-map)# set transform-set IntraNet
Branch(config-crypto-map)# match address 110
Branch(config-crypto-map)# reverse-route 사설구간을 eigrp에 선언하지 않았으므로 반드시 이 설정이 필요하다.
Branch(config-crypto-map)# exit
■ HEAD-1 라우터
HEAD-1(config)# access-list 110 permit ip 192.168.20.0 0.0.0.255 192.168.10.0 0.0.0.255
HEAD-1(config)# crypto ipsec transform-set IntraNet ah-sha-hmac esp-aes 128
HEAD-1(cfg-crypto-trans)# exit
HEAD-1(config)#
HEAD-1(config)# crypto map To-Branch 10 ipsec-isakmp
HEAD-1(config-crypto-map)# set peer 100.10.10.2
HEAD-1(config-crypto-map)# set transform-set IntraNet
HEAD-1(config-crypto-map)# match address 110
HEAD-1(config-crypto-map)# reverse-route 사설구간을 eigrp에 선언하지 않았으므로 반드시 이 설정이 필요하다.
HEAD-1(config-crypto-map)# exit
HEAD-1(config)#
■ HEAD-2 라우터
HEAD-2(config)# access-list 110 permit ip 192.168.20.0 0.0.0.255 192.168.10.0 0.0.0.255
HEAD-2(config)# crypto ipsec transform-set IntraNet ah-sha-hmac esp-aes 128
HEAD-2(cfg-crypto-trans)# exit
HEAD-2(config)#
HEAD-2(config)# crypto map To-Branch 10 ipsec-isakmp
HEAD-2(config-crypto-map)# set peer 100.10.10.2
HEAD-2(config-crypto-map)# set transform-set IntraNet
HEAD-2(config-crypto-map)# match address 110
HEAD-2(config-crypto-map)# reverse-route 사설구간을 eigrp에 선언하지 않았으므로 반드시 이 설정이 필요하다.
HEAD-2(config-crypto-map)# exit
HEAD-2(config)#
4. IPsec VPN 설정을 interface에 적용
■ Branch 라우터 IPsec VPN 설정을 interface에 적용
Branch(config)# interface ethernet 0/1
Branch(config-if)# crypto map To-HEAD
Branch(config-if)# exit
■ HEAD-1 라우터 VPN 설정을 interface에 적용
HEAD-1(config)# interface ethernet 0/0
HEAD-1(config-if)# crypto map To-Branch
HEAD-1(config-if)# exit
■ HEAD-2 라우터 VPN 설정을 interface에 적용
HEAD-2(config)# interface ethernet 0/0
HEAD-2(config-if)# crypto map To-Branch
HEAD-2(config-if)# exit
5. 192.168.20.0/24 네트워크에서 출발하는 트래픽을 위한 HSRP 설정
■ HEAD-1 라우터
HEAD-1(config)# interface ethernet 0/1
HEAD-1(config-if)# standby 1 ip 192.168.20.254
HEAD-1(config-if)# standby 1 priority 120
HEAD-1(config-if)# standby 1 preempt
HEAD-1(config-if)# standby 1 track ethernet 0/0 50
HEAD-1(config-if)# exit
■ HSRP 설정 : HEAD-2 라우터
HEAD-2(config)# interface ethernet 0/1
HEAD-2(config-if)# standby 1 ip 192.168.20.254
HEAD-2(config-if)# standby 1 preempt
HEAD-2(config-if)# standby 1 track ethernet 0/0
HEAD-2(config-if)# exit
6. 192.168.10.0/24 네트워크에서 출발하는 트래픽을 위한 HSRP 설정
■ VPN 이중화 설정 : HEAD-1 라우터
HEAD-1(config)# interface ethernet 0/0
HEAD-1(config-if)# standby 2 ip 100.10.20.254
HEAD-1(config-if)# standby 2 preempt
HEAD-1(config-if)# standby 2 name VPN
HEAD-1(config-if)# standby 2 track ethernet 0/1
HEAD-1(config-if)# crypto map To-Branch redundancy VPN
HEAD-1(config-if)# exit
■ VPN 이중화 설정 : HEAD-2 라우터
HEAD-2(config)# interface ethernet 0/0
HEAD-2(config-if)# standby 2 ip 100.10.20.254
HEAD-2(config-if)# standby 2 priority 120
HEAD-2(config-if)# standby 2 name VPN
HEAD-2(config-if)# standby 2 track ethernet 0/1 50
HEAD-2(config-if)# crypto map To-Branch redundancy VPN
HEAD-2(config-if)# exit
■ 라우팅 테이블 확인
Branch# show ip route
...중략
100.0.0.0/24 is subnetted, 2 subnets
C 100.10.10.0 is directly connected, Ethernet0/0
D 100.10.20.0 [90/307200] via 100.10.10.1, 00:15:01, Ethernet0/0
C 192.168.10.0/24 is directly connected, Ethernet0/1
S 192.168.20.0/24 [1/0] via 100.10.20.254 crypto map 설정시 “reverse-route”명령에 의해 생성된 static 경로
Branch#
HEAD-1# show ip route
...중략
100.0.0.0/24 is subnetted, 2 subnets
D 100.10.10.0 [90/307200] via 100.10.20.1, 00:14:23, Ethernet0/0
C 100.10.20.0 is directly connected, Ethernet0/0
S 192.168.10.0/24 [1/0] via 100.10.10.2 crypto map 설정시 “reverse-route”명령에 의해 생성된 static 경로
C 192.168.20.0/24 is directly connected, Ethernet0/1
HEAD-2# show ip route
...중략
100.0.0.0/24 is subnetted, 2 subnets
D 100.10.10.0 [90/307200] via 100.10.20.1, 00:17:12, Ethernet0/0
C 100.10.20.0 is directly connected, Ethernet0/0
S 192.168.10.0/24 [1/0] via 100.10.10.2 crypto map 설정시 “reverse-route”명령에 의해 생성된 static 경로
C 192.168.20.0/24 is directly connected, Ethernet0/1
HEAD-2#
■ HSRP 설정 확인
HEAD-1# show standby brief
P indicates configured to preempt.
|
Interface Grp Prio P State Active Standby Virtual IP
Et0/0 2 100 P Standby 100.10.20.3 local 100.10.20.254
Et0/1 1 110 P Active local 192.168.20.2 192.168.20.254
HEAD-1#
HEAD-2# show standby brief
P indicates configured to preempt.
|
Interface Grp Prio P State Active Standby Virtual IP
Et0/0 2 110 P Active local 100.10.20.2 100.10.20.254
Et0/1 1 100 P Standby 192.168.20.1 local 192.168.20.254
HEAD-2#
■ IPsec VPN 설정 확인
HEAD-1# show crypto map
Crypto Map "To-Branch" 10 ipsec-isakmp
Peer = 100.10.10.2
Extended IP access list 110
access-list 110 permit ip 192.168.20.0 0.0.0.255 192.168.10.0 0.0.0.255
Current peer: 100.10.10.2
Security association lifetime: 4608000 kilobytes/3600 seconds
PFS (Y/N): N
Transform sets={
IntraNet,
}
Reverse Route Injection Enabled
Interfaces using crypto map To-Branch:
Ethernet0/0
HEAD-1#
HEAD-2# show crypto map
Crypto Map "To-Branch" 10 ipsec-isakmp
Peer = 100.10.10.2
Extended IP access list 110
access-list 110 permit ip 192.168.20.0 0.0.0.255 192.168.10.0 0.0.0.255
Current peer: 100.10.10.2
Security association lifetime: 4608000 kilobytes/3600 seconds
PFS (Y/N): N
Transform sets={
IntraNet,
}
Reverse Route Injection Enabled
Interfaces using crypto map To-Branch:
Ethernet0/0
HEAD-2#
[출처] IPsec VPN - HSRP|작성자 HOONY


































