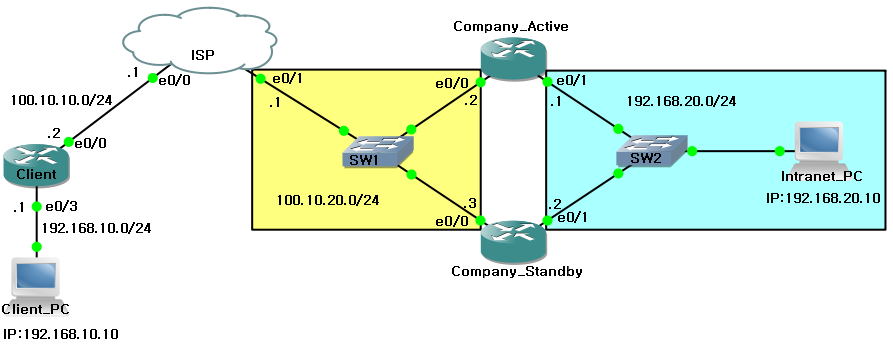
IPsec VPN - HSRP 2중 경로
VPN을 구성함에 있어 하나의 경로로만 구성하면 안정성이 낮아진다.
그러므로, Intranet을 위한 VPN에 HSRP를 활용하여 이중화를 하여 안정성을 높일 수 있다.
Company_Active 라우터가 192.168.20.0/24 네트워크에 대하여 Active 상태로 작동하고
Company_Stanby 라우터는 Standby 상태로 대기중이다.
그러다가 Company_Active의 ethernet 0/1포트에 장애가 발생하면 Company_Stanby 라우터가
preempt에 의해 권한은 위임받아 Active 상태가 된다.
■ Client 라우터 기본 설정
Router(config)#
hostname Client
Client(config)# interface
ethernet 0/3
Client(config-if)# ip address
192.168.10.1 255.255.255.0
Client(config-if)# no
shutdown
Client(config-if)#
exit
Client(config)# interface
ethernet 0/0
Client(config-if)# ip address
100.10.10.2 255.255.255.0
Client(config-if)# no
shutdown
Client(config-if)#
exit
Client(config)# router eigrp
10
Client(config-router)# no
auto-summary
Client(config-router)# network
100.10.10.0
Client(config-router)# network
192.168.10.0
Client(config-router)#
exit
Client(config)#
■ Company_Active 라우터 기본 설정
Router(config)#
hostname Company_Active
Company_Active(config)#
interface ethernet 0/0
Company_Active(config-if)# ip
address 100.10.20.2 255.255.255.0
Company_Active(config-if)# no
shutdown
Company_Active(config-if)#
exit
Company_Active(config)#
interface ethernet 0/1
Company_Active(config-if)# ip
address 192.168.20.1 255.255.255.0
Company_Active(config-if)# no
shutdown
Company_Active(config-if)#
exit
Company_Active(config)# router
eigrp 10
Company_Active(config-router)#
no auto-summary
Company_Active(config-router)#
network 100.10.20.0
Company_Active(config-router)#
network 192.168.20.0
Company_Active(config-router)#
exit
Company_Active(config)#
■ Company_Standby 라우터 기본 설정
Router(config)#
hostname Company_Standby
Company_Standby(config)#
interface ethernet 0/0
Company_Standby(config-if)# ip
address 100.10.20.3 255.255.255.0
Company_Standby(config-if)# no
shutdown
Company_Standby(config-if)#
exit
Company_Standby(config)#
interface ethernet 0/1
Company_Standby(config-if)# ip
address 192.168.20.2 255.255.255.0
Company_Standby(config-if)# no
shutdown
Company_Standby(config-if)#
exit
Company_Standby(config)#
router eigrp 10
Company_Standby(config-router)#
no auto-summary
Company_Standby(config-router)#
network 100.10.20.0
Company_Standby(config-router)#
network 192.168.20.0
Company_Standby(config-router)#
exit
■ ISP 라우터 기본 설정
Router(config)#
hostname ISP
ISP(config)# interface
ethernet 0/0
ISP(config-if)# ip address
100.10.10.1 255.255.255.0
ISP(config-if)# no
shutdown
ISP(config-if)#
exit
ISP(config)# interface
ethernet 0/1
ISP(config-if)# ip address
100.10.20.1 255.255.255.0
ISP(config-if)# no
shutdown
ISP(config-if)#
exit
ISP(config)# router eigrp
10
ISP(config-router)# no
auto-summary
ISP(config-router)# network
100.10.10.0
ISP(config-router)# network
100.10.20.0
ISP(config-router)#
exit
ISP(config)# exit
ISP#show ip
route
Codes: C
- connected, S - static, R - RIP, M - mobile, B - BGP
D - EIGRP, EX - EIGRP
external, O - OSPF, IA - OSPF inter area
N1 - OSPF NSSA external
type 1, N2 - OSPF NSSA external type 2
E1 - OSPF external type
1, E2 - OSPF external type 2
i - IS-IS, su - IS-IS
summary, L1 - IS-IS level-1, L2 - IS-IS level-2
ia - IS-IS inter area,
* - candidate default, U - per-user static route
o - ODR, P - periodic
downloaded static route
Gateway of last resort is not set
100.0.0.0/24 is
subnetted, 2 subnets
C 100.10.10.0 is
directly connected, Ethernet0/0
C 100.10.20.0 is
directly connected, Ethernet0/1
D 192.168.10.0/24
[90/307200] via 100.10.10.2, 00:01:53, Ethernet0/0
D
192.168.20.0/24 [90/307200] via 100.10.20.3, 00:01:36,
Ethernet0/1
[90/307200] via 100.10.20.2, 00:01:36, Ethernet0/1
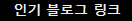
Intranet의
192.168.20.0/24 네트워크에 대한 경로가 2중으로 설정되었다.
----------------------------------------------------------------
게이트웨이 이중화 설정 - SDM 접속을 위하여 로컬 계정을 추가한다.
----------------------------------------------------------------
■ HSRP 설정 - Company_Standby 라우터
Company_Standby(config)#
username Hoony privilege 15 password 0 1234
Company_Standby(config)#
interface ethernet 0/1
Company_Standby(config-if)#
standby 1 ip 192.168.20.254
Company_Standby(config-if)#
standby 1 preempt
Company_Standby(config-if)#
standby 1 track ethernet 0/0
Company_Standby(config-if)#
exit
Company_Standby(config)#
exit
Jan 19
13:48:44.239: %HSRP-6-STATECHANGE: Ethernet0/1 Grp 1 state Standby ->
Active
Jan 19
13:48:47.259: %HSRP-6-STATECHANGE: Ethernet0/1 Grp 1 state Active ->
Speak
Company_Standby#
show standby brief
P indicates configured to preempt.
|
Interface
Grp Prio P State Active Standby Virtual IP
Et0/1
1 100 P Standby 192.168.20.1 local 192.168.20.254
Company_Standby#
■ HSRP 설정 - Company_Active 라우터
Company_Active(config)#
username Hoony privilege 15 password 0 1234
Company_Active(config)#
interface ethernet 0/1
Company_Active(config-if)#
standby 1 ip 192.168.20.254
Company_Active(config-if)#
standby 1 priority 150
Company_Active(config-if)#
standby 1 preempt
Company_Active(config-if)#
standby 1 track ethernet 0/0 60
Company_Active(config-if)#
exit
Company_Active(config)#exit
Jan
19 13:48:56.131: %HSRP-6-STATECHANGE: Ethernet0/1 Grp 1 state Listen ->
Active
Company_Active#
show standby brief
P indicates configured to preempt.
|
Interface
Grp Prio P State Active Standby Virtual IP
Et0/1
1 150 P Active local 192.168.20.2 192.168.20.254
Company_Active#
■ SDM을 이용한 IPsec VPN 서버 설정
■ VPN Client 프로그램을 이용한 Intranet (192.168.20.0/24) 접속
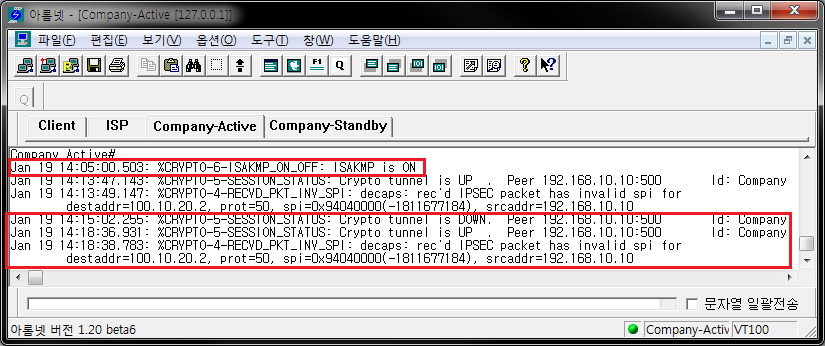
■ isakmp on 상태 및 VPN client 접속 완료
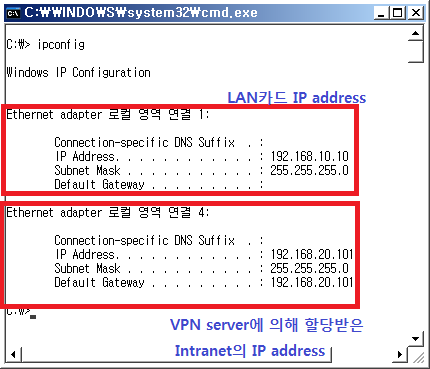
■ 사설 Intranet 의 IP를 할당 받은 상태 확인
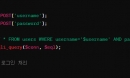
■ show running-config - Company-Active 라우터
...중략
username Hoony privilege 15 password
0 1234
!
aaa new-model
aaa authentication login default
local
aaa authentication
login sdm_vpn_xauth_ml_1 local
aaa authorization exec default local
aaa authorization network
sdm_vpn_group_ml_1 local
aaa
session-id common
!
crypto isakmp policy 1
encr 3des
authentication pre-share
group 2
crypto isakmp xauth timeout 15
!
crypto isakmp client configuration group
Company
key
123123
pool
SDM_POOL_1
max-users
20
!
crypto ipsec transform-set ESP-3DES-SHA
esp-3des esp-sha-hmac
!
crypto dynamic-map SDM_DYNMAP_1
1
set transform-set
ESP-3DES-SHA
reverse-route
!
crypto map SDM_CMAP_1 client authentication
list sdm_vpn_xauth_ml_1
crypto
map SDM_CMAP_1 isakmp authorization list sdm_vpn_group_ml_1
crypto map SDM_CMAP_1 client configuration
address respond
crypto map
SDM_CMAP_1 65535 ipsec-isakmp dynamic SDM_DYNMAP_1
!
interface Ethernet0/0
ip address 100.10.20.2
255.255.255.0
half-duplex
crypto map SDM_CMAP_1
!
ip local pool SDM_POOL_1 192.168.20.100
192.168.20.150
ip http
server































![뚜따에 진심인 형+과학자코스프레+현미경을구입했어 [정종철] 뚜따에 진심인 형+과학자코스프레+현미경을구입했어
CPU 뚜따 교육자료ㅋㅋ](https://raptor-hw.net/xe/files/thumbnails/739/203/241x165.crop.jpg)